12/11/2024
CTI
Adversarial perspective on AI
Cybersecurity Insights
AI became a facilitator for the proper conduct of cybercriminal business. The resilience required within diverse organizations to respond to cybersecurity imperatives is also clearly visible on the dark side. It enables threat actors to develop malicious products capable to adapt by capitalizing on their success but also to bounce back in the event of confrontation with efficient defense systems. The match goes on in this last episode of the CWATCH AI series.
Using AI for defence evasion
AI can be more discreet than a big audit script and faster than a human.
More and more threat actors understand the benefits brought by AI to enhance their performance and increase their revenue. One of the most interesting aspects is how AI can significantly improve their camouflage as the detection of their activities can interfere with their survey of new victims and impede the potentiality of new damages.
Main possibilities offered by AI
EXPLOIT ENCRYPTION
FILELESS ATTACKS
MALWARE CREATION
Scripting to better select data
Elaborate social engineering attacks accordingly
Disable security features or even evade them.
A new grammar for threat actors
AI can be more discreet than a big audit script and faster than a human.
Artificial intelligence is enhancing reconnaissance, intelligence gathering and offensive capabilities on the dark side. Threat actors exploit LLM to gather information, including sensitive ones on their victims more effectively.
Make expandable bombs
Developing dynamic payloads that, during an attack, can change their behaviour or load more malware which allows adjusting in real time to the victim’s environment and load more modules or tools according to that.
All in all, carry out several tasks at once and increase the power of ongoing attacks.
Threat actors’ favourite LLM

Not leaving any trace
Adaptive network traffic analysis techniques may change their behaviour to avoid detection are being created using AI. These alterations are designed to mix harmful traffic with the natural flow of legitimate network communications, creating difficulties in detection.

Flexible malicious products
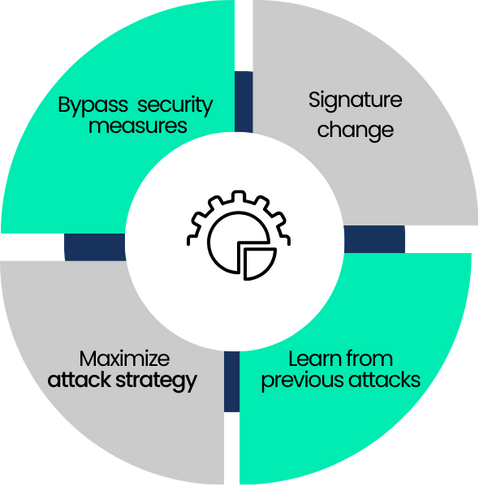
Continuous improvement
AI allows threat actors to continuously improve their attacks by adapting to security systems in real time. Modifying tactics during an ongoing attack based on analysis of the target’s defences.
Malware produced by AI is described as having generative capabilities and intelligent automation mechanisms that can adjust malware to evade detection.
For example, researchers created new malware variants that were skilled at avoiding detection using AI-generated code and a malware that was able to destroy innocuous command and control channels.
Some malware with an AI core have self-healing features that enable it to regenerate missing components, repair itself after removal attempts, and adjust to new protection measures.
Adaptive malware characteristics
Adaptive malware characteristics
Code adjusted for malicious activities able to avoid detection.
Rewriting the code of already well-known malware by adding obfuscation.
Each attack employs a novel obfuscation technique, rendering any detection based on code or process execution patterns ineffective.
Code pattern-based detection methods can be circumvented by the capability to significantly obscure code at will. By grasping the methods through which security instruments identify abnormal actions, threat actors employ LLM to devise tactics that resemble typical user behaviour, thereby evading detection.